Blog > What Is Cybercrime and How Can It Affect Your Business?
What Is Cybercrime and How Can It Affect Your Business?
In 2001, the Internet was still in its early stages of growth and acceptance. Back then, most online purchases were paid for by money order. By 2014, consumers had shifted to credit and debit cards for nearly 80% of all online transactions.
As technology advances, criminals are working just as hard to keep up. Last year alone, cybercrime cost U.S. businesses a total of $1 billion.
While business owners can’t ensure complete immunity from cybercrime, certain protective measures could drastically enhance overall security.
What is Cybercrime?
Cybercrime is any crime that involves a computer or computer network and takes place via the Internet. Cybercriminals use computers to steal personal or business information. This includes confidential documents and data stored on a computer network. Once cybercriminals have obtained this information, they can expose private security information or use it for financial gain at the expense of the business.
Types of Cybercrime
Cybercriminals can attack businesses from various angles. Be on the lookout for some of these forms of cybercrime:
Identity Theft
It’s not just for individual people anymore. Since banks and creditors are not legally required to cover financial losses, criminals can steal a business’s identity to establish credit with banks or retailers. Consequentially, 60% of businesses that fall victim to identity theft shut down within 1 year.
Hacking
Criminals use numerous types of software to break into a business’ computer network and steal personal and customer information. Hackers need to have advanced computer knowledge to sort through complicated codes and algorithms in order to identify details about a network. Businesses may not even be aware the theft is happening, because data is being secretly retrieved from an isolated location.
Cyberstalking
Generally, this happens when an individual uses the Internet to stalk someone, sometimes in a harmful or threatening way. An individual may terrorize a company for financial gain or plot revenge on a former employer. Spyware can give access to private computer or cellular business information.
Phishing
Criminals trick business owners into giving away vital information. Oftentimes, they send emails that look like they originate from a bank or credit card company and ask the recipient to verify personal credentials. Look to the domain name for clues. Phishers will often use subdomains, something legitimate companies would never do. For example, a link in an email that looks like one from Chase Bank might send you to bank.chase.com instead of chase.com.
File Hijacking
A file hijacker is a virus that seizes data files from a PC and encrypts them. Hackers can then hold the files ransom until requested payment is received. Viruses can be acquired through e-mails or websites that are infected with the virus. Only the most current security software can keep a business safe from file hijacking.
Keylogging
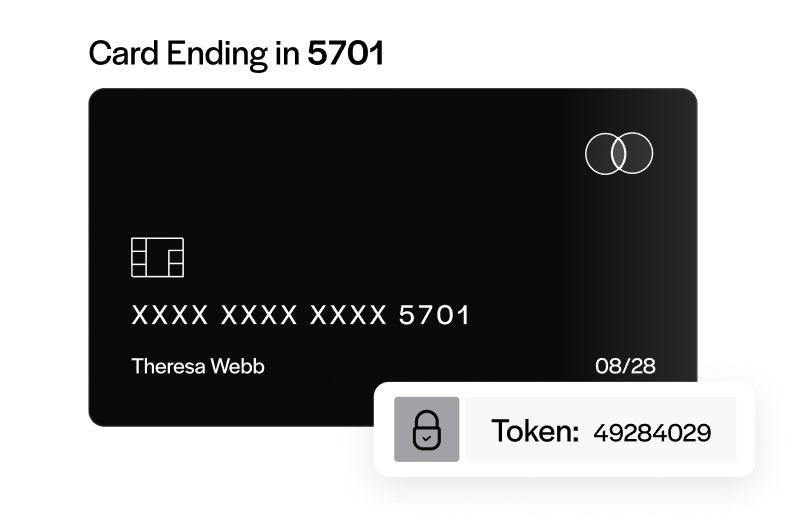
Criminals implement a software or device to gain access to every keystroke made on an individual keyboard. Targeted business owners give away valuable usernames, passwords, or account numbers without even knowing it.
How to Defend Against Cybercrime
Implementing these measures will lower your risk of becoming a hacker’s next victim. Do what you can to protect your business!
Install Security Software
High-quality anti-virus software is an investment that can safeguard critical business information and keep it out of the wrong hands.
Avoid Suspicious Emails
Don’t open emails from unfamiliar senders.
Never submit passwords or PIN numbers via email requests.
Check the domain name. Never trust content delivered by subdomains.
Check Bank Statements Frequently
Report suspicious activity immediately.
Be aware of business purchases. Prompt action at the onset of cybercrime can greatly reduce the risk of further damages.
Make Sure Your Computer is Current With Updates
Keep your software up to date with regular fixes to help block hackers from accessing business data.